KALI – How to crack passwords using Hashcat – The Visual Guide
Windows passwords are stored as MD5 hashes, that can be cracked using Hashcat. There is a Windows 10 password hacking version here:
https://wordpress.com/stats/post/4497/uwnthesis.wordpress.com
Step 1 – Root terminal
mkdir hashes
cd /hashes
gedit hashes.txt
This organises a hashes directory for you, and a hashes.txt file which will contain the hashes to be cracked.
*****
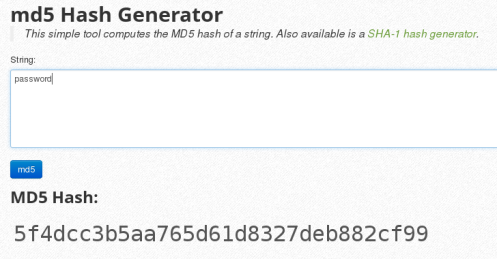
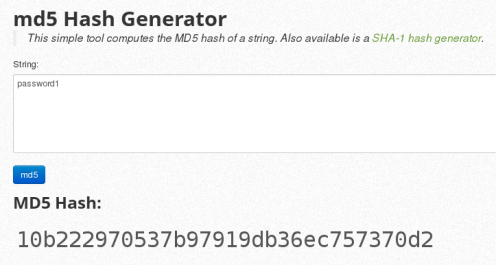
Step 2 – Generate hashes for you to crack
http://www.miraclesalad.com/webtools/md5.php
Hashes.txt is the file of password hashes to be cracked – we’ll create hashes to paste into this file.
To generate hashes, use:
http://www.miraclesalad.com/webtools/md5.php
Enter the word “password” – and the site will return the MD5 hash, paste it into the hashes.txt
Next, hash a second password ie “password1”, paste the md5 hashes into hashes.txt.
Fill up your hashes.txt with five test md5 hashes.
This is your test hash file complete. Now we move into attack mode.
******
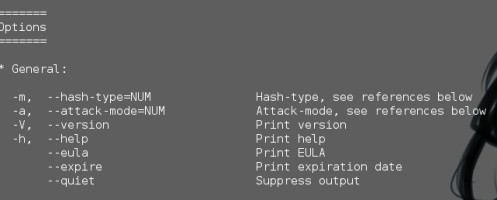
Hashcat options. Jump to step 4 – to attack.
This is background information so that you can adapt your attack for windows hashes or unix hashes etc.
hashcat –help
-m = hash type (the hash varies by operating system)
-a = Attack Mode (we’ll use both Straight and Combination Attack)
-r = rules file (look for xyz.rule)
******
ATTACK CODE:
(Carries out a straight through attack against MD5 hashes using the rockyou dictionary).
hashcat -m 0 -a 0 /root/hashes/hashes.txt /root/rockyou.txt
*********
Attack Modes – just for reference
-a 0 (Each number is a DIFFERENT attack mode)
0 = Straight
1 = Combination
2 = Toggle case
3 = Brute Force
 I’ve found that straight or -a 0 is ridiculously fast on simple passwords.
I’ve found that straight or -a 0 is ridiculously fast on simple passwords.
You have been warned.
******
Hash Type – Just for reference
The operating system determines the hash used. You need to know the hash type.
Unix = MD5 hash
Kali = SHA512 hash
Windows XP = LM Hash
Windows 7 = NTLM Hash
-m 0 (Each number is a different Hash Type)
0 = MD5 hash…. so we use -m 0
50 = HMAC-MD5….so we use -m 50
1000 = NTLM….so we use -m 1000
*****
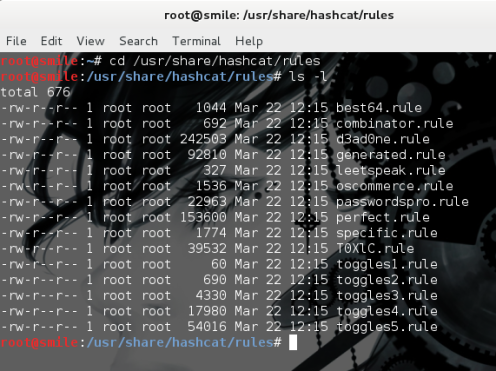
Step 3 – Locate password database for the attack
To locate the Rockyou password database in KALI type:
locate *rock*
To locate Hashcat Rules files
cd /usr/share/hashcat/rules
ls -l
You can gedit each rule file to read it if you wish…. that’s a great way to learn more about hashcat 🙂
*****
Step 4 – the REAL ATTACK code
hashcat -m 0 -a 1 /root/hashes/hashes.txt /root/rockyou.txt
(to launch a combination attack against MD5 password hashes)
or
hashcat -m 0 -a 0 /root/hashes/hashes.txt /root/rockyou.txt
(a straight through attack is super fast on simple passwords)
*****
The attack looks like this:
The hashes are shown – with the plain text password given next to it.
The Rockyou database has several million passwords, but if it’s not in there, then it won’t be cracked.
The 2 major cracking dictionaries are Rockyou, and CrackStation.
Rockyou contains 14 million unique passwords.
CrackStation. For MD5 and SHA1 hashes, there is a 190GB, 15-billion-entry lookup table, and for other hashes, they offer a 19GB 1.5-billion-entry lookup table.
Download CrackStation by Torrent:
https://crackstation.net/buy-crackstation-wordlist-password-cracking-dictionary.htm
****
Free Rainbow Tables can also be found here (lots of them)
https://www.freerainbowtables.com/en/tables2/
Some hashes will fail to be cracked, this is due to several reasons, it may not be a md5 hash, it may not be in your password list etc.
Hashes are case sensitive, so Password1 is not the same as password1.
oclHashcat-Plus uses your GPU rather than your CPU to crack passwords. Graphics cards are MUCH faster as an attack tool, than a CPU… MANY times faster.
Cryptography
Hash Lengths
| HASH | SIZE |
|---|---|
| MD5 Hash Length | 16 Bytes |
| SHA-1 Hash Length | 20 Bytes |
| SHA-256 Hash Length | 32 Bytes |
| SHA-512 Hash Length | 64 Bytes |
Hash Examples
Likely just use hash-identifier for this but here are some example hashes:
| HASH | EXAMPLE |
|---|---|
| MD5 Hash Example | 8743b52063cd84097a65d1633f5c74f5 |
| MD5 $PASS:$SALT Example | 01dfae6e5d4d90d9892622325959afbe:7050461 |
| MD5 $SALT:$PASS | f0fda58630310a6dd91a7d8f0a4ceda2:4225637426 |
| SHA1 Hash Example | b89eaac7e61417341b710b727768294d0e6a277b |
| SHA1 $PASS:$SALT | 2fc5a684737ce1bf7b3b239df432416e0dd07357:2014 |
| SHA1 $SALT:$PASS | cac35ec206d868b7d7cb0b55f31d9425b075082b:5363620024 |
| SHA-256 | 127e6fbfe24a750e72930c220a8e138275656b |
| SHA-256 $PASS:$SALT | c73d08de890479518ed60cf670d17faa26a4a7 |
| SHA-256 $SALT:$PASS | eb368a2dfd38b405f014118c7d9747fcc97f4 |
| SHA-512 | 82a9dda829eb7f8ffe9fbe49e45d47d2dad9 |
| SHA-512 $PASS:$SALT | e5c3ede3e49fb86592fb03f471c35ba13e8 |
| SHA-512 $SALT:$PASS | 976b451818634a1e2acba682da3fd6ef |
| NTLM Hash Example | b4b9b02e6f09a9bd760f388b67351e2b |
Reference
How to crack Oracle Passwords
*****
Password hacking / password cracking – http://www.hashkiller.co.uk
https://uwnthesis.wordpress.com/2016/06/12/password-hacking-password-cracking-www-hashkiller-co-uk/
BRUTE FORCE HACKING – Brute force Calculator – A Visual Guide
https://uwnthesis.wordpress.com/2014/04/18/bruteforce-hacking-bruteforce-calculator-a-visual-guide/
*****
SupraFortix – Hashcat Password Cracking – Uni South Wales blog
http://suprafortix.wordpress.com/2014/06/13/hashcat-password-craking/
KALI – First things to do after installing Kali Debian Linux – The Visual Guide
How to write a password that takes over 35 quadrillion years to crack (but is easy to remember)
Trackbacks & Pingbacks
- BRUTEFORCE HACKING – Bruteforce Calculator – A Visual Guide | University of South Wales: Information Security and Privacy
- BRUTEFORCE HACKING Bruteforce Calculator A Visual Guide … – News4Security
- University of South Wales: Posts about KALI | Người Đến Từ Bình Dương
- How to crack passwords on Windows 7 – Hashcat | University of South Wales: Information Security and Privacy
- How to crack passwords using a GUI on Windows 7 – Hashcat ... - News4Security
- Password Cracking – What is a password hash? | University of South Wales: Information Security and Privacy
- How to get same crypt(3) function in Mac OS X as Linux gcc/gnu crypt(3)? Linux gcc crypt(3) has MD5 and SHA512. Apple Gcc crypt(3) *only* uses DES - BlogoSfera
- KALI – How to crack passwords using Hashcat – The Visual Guide | LUG Mureş
- Password hacking / password cracking – www.hashkiller.co.uk | University of South Wales: Information Security for Privacy
- Hashing Password with Bcrypt – NHR InfoSec and Software Development
- Yahoo reveals yet another billion-user breach – Technology Spoon
- Yahoo reveals yet another billion-user breach – Darby's
- Yahoo reveals yet another billion-user breach | Easy notes
- Yahoo reveals yet another billion-user breach | Daily Rant Online
- Yahoo reveals yet another billion-user breach | MyFads
- Yahoo reveals yet another billion-user breach – TheNycPlug
- Yahoo reveals yet another billion-user breach | Intelligent Jamaica
- Yahoo reveals yet another billion-user breach - techietricks.com
- Yahoo reveals yet another billion-user breach | ZERO DAY TECH
- Yahoo reveals yet another billion-user breach | Jamaican Moments™
- Tech Connecto - Let's Talk Tech
- Yahoo reveals yet another billion-user breach – The Verge | Newsist
- Hashcat Tutorial for Beginners
- Hashcat Tutorial for Beginners - Infosec Resources > Seekalgo
- Hashcat Tutorial for Beginners [updated 2021] – Sharefun
- Hashcat Tutorial for Beginners [updated 2021] – hacker files z093.com
- Hashcat Tutorial for Beginners








Reblogged this on oogenhand and commented:
Very important.
LikeLike
A very helpful article brilliantly illustrated.
Good work! Cheers
LikeLike
Reblogged this on Người Đến Từ Bình Dương.
LikeLike
A very good post.
You can find a new sorted & uniq dictionary list for hashcat && jtr. DCHTPassv1.0 is available. Check it out and Enjoy!
LikeLike
Hi , I have been attempting this for the last hour! Please help! I am able to load the 5 hashes into the hashes.txt file , but when I go to run the attack I recieve the error msg :
/root/rockyou.txt: No such file or directory.
Thank you in advance .
LikeLike
Hi Tyler
If you search for the standard location of the rockyou dictionary, you’ll find the original path on Kali.
*rockyou*.* – and it’ll reveal the full path.
As I’m lazy, I copied the file over to /root/rockyou.txt. that’s so the rockyou dictionary is always easy to find. Sorry if I caused you any confusion.
LikeLike
thanks for the reply uwnthesis. I was able to locate the rockyou file, when i am running the tests i receive the following:
Input.Mode : Dict ( /usr/share/hashcat/rules/rockyou-30000.rule)
Index….: 1/1 (segment), 30000 (words), 331161 (bytes)
Recovered : 0/5 hashes, 0/1 salts
Speed/sec . : 5.29M Plains, 176 words
Progress : 30000/30000 (100%)
Estimated time / . —
[s]tatus [p]ause [r]esume [b]ypass [q]uit =>
Am Doing the attack right because it doesn’t seem to be recovering any passwords from the hashes!
Thanks for your help, i am fairly new with all this but am super intrigued! thanks again.
LikeLike
Hi Tyler,
Try making up your own hashes file for easy passwords like password, password123. Then run hashcat against these easy passwords to get a feel for how the system works.
Use the MD5 hashes from http://www.miraclesalad.com/webtools/md5.php to create your md5 hashes file.
Go for a nice easy attack, such as the straight thru attack
hashcat -m 0 -a 0 hashes.txt rockyou.txt
-m 0 = md5 hashes
-a 0 = straight through attack
Good luck! Password cracking is very addictive – so you’ll have lots of fun.
LikeLike
Hey again.
I was able to get all of my hashes stored into the file hashes.txt and run the atttack
hashcat -m 0 -a 0 /hashes/hashes.txt /usr/share/hashcat/rules/rockyou-30000.rule
when i locate *rockyou* , it tells me that the file is the /usr/share/hashcat/rules/rockyou-30000.rule so i figured thats where i should execute the attack from however it seems to load all 5 hashes, but doesn’t seem to run. This is what happens when i run the attack.
Initizialing hashcat v2.00 with 1 thread and 32 mb segment size…
Added hashes from file /hashes/hashes.txt : 5 (1 salts)
[s]tatus [p]ause [r]esume [b]ypass [q]uit =>
Input.Mode: Dict (/usr/share/hashcat/rules/rockyou-30000.rule)
Index…. : 1/1 (segment), 30000 (words), 331161 (bytes)
Recovered: 0/5 hashes, 0/1 salts
Speed/sec : – plains, – words
Progress : 30000/30000 (100%)
Running : –: –: –: —
Estimated –: –: –: —
Started : Wed Mar 23 19:13:52 2016
Stopped: Wed Mar 23 19:13:53 2016
Am i doing everything correct and maybe its my virtual kali machine that is installed improperly? Anyway to re install it from scratch?
Thanks again for your help and time, it is greatly appreciated from a noobie! 🙂
Cheers,
Tyler
LikeLike
Hi uwnthesis, I was able to crack the hashes! What a relief and great feeling! I am now looking at hacking wireless networks but do not have a wireless card or adapter.
I am running kali linux via virtualbox on a macbook air. I am curious what your recommendation would be for a wirless adapater? I have been reading a lot on the Kali forum but have found it fairly confusing! I want to be able to just plug in the adapater and enable monitor mode so i can scan for networks!
Thanks again for your help uwnthesis, you are the best!
Cheers,
Tyler
LikeLike
Hi Tyler,
Cracking Wifi is great fun. The first rule is to use a wifi adapter that is compatible with Kali. Most hackers would recommended the Alfa range.
You’ll need a high gain antenna to reach longer distances. You can use an Alfa paddle or 7 db gain antenna – or an Alfa adapter that has 2 antennas on it.
Alfa have drivers for Kali.
You need to be careful about the network adapter you select.
1. Must work with Kali
2. Must be capable of packet injection.
The easiest tool to use is Fern for wifi hacking. It’s very easy to use.
The tool I really like is Wifite – this is an auditing tool and will carry out packet injection for you. It will colour code the wifi – so you’ll know if your signal is strong enough.
Transmission power is an important part of hacking. You can alter the country code to remove regulations, eg if you set the country code to BO for Bolivia all restrictions on transmission power would be removed.
The easiest way to hack is to use Fern, and go for WPS cracking to start off with.
Have fun!
LikeLike
Thank you so much for the reply! I will let you know if I encounter any problems along the way!
LikeLike
would something like this work? https://www.amazon.ca/TP-LINK-TL-WN822N-Wireless-External-Antennas/dp/B00416Q5KI/ref=dp_ob_title_ce
thanks.
LikeLike
Hi Tyler,
The “bunny ears” adapter – one of my all time favourite adapter.
Sorry no, this can’t carry out packet injection – which is what you need to hack wifi.
But the bunny ears adapter is a very good, fast, and stable network adapter.
This alfa adapter is *very* old, but it was one of the best adapters.
Selecting the right adapter is a very important step. Get the wrong adapter and all the hacking tools will fail on you.
You might be able to get a second hand AWUS036H to experiment with thats very cheap.
But it’s only 54 mpbs. It will be very limited and old school, however this was an amazing adapter for Kali – a legendary network adapter to be honest, as it picked up so many networks.
LikeLike
Thanks again for your help in finding the right adapter! I am in Canada so that one does not ship to Canada! But I managed to find 3 on amazon.ca 😉 Here are the three that seem similar. let me know which one you recommend!
Thanks a bunch!
Tyler
LikeLike
Hi Tyler,
Are you able to get this adapter locally?
http://www.blackhackwireless.com/collections/top-kali-wireless-adapters/products/alfa-awuso36neh-atheros-ar9271-chipset
Remember to get a good high gain antenna to go with it if you’ve any extra cash. Alfa make a
7db paddle
10 db panel antenna
http://www.amazon.co.uk/Network-APA-M04-directional-antenna-connector/dp/B003ZWILOW?ie=UTF8&keywords=alfa%20antenna&qid=1459005122&ref_=sr_1_4&sr=8-4
Every 3db is a doubling in signal strength. So 7 db or 10 db is a *big* different in picking up wifi – the 7db paddle is often used for war driving. The 10 db antenna is great for using in hostile environments – even got it working inside a giant faraday cage. Wifi hacking is amazing fun – and you’ll get to use all these skills in the workplace too.
LikeLike
As I’m in Canada , the one you recommend doesn’t ship to Canada! Here are 3 alternatives that I think are similar to the one you suggested!
Thank you for your help !
Tyler
LikeLike
No problem with helping! I’ve been exactly where you are.. and opted for a more expensive wifi adapter – which totally failed. Hopefully I can guide you, so that you don’t waste any money.
The key to wifi hacking is the chipset inside the wifi adapter.
http://www.wirelesshack.org/top-kali-linux-compatible-usb-adapters-dongles-2015.html
Here are the most common chipsets used with Kali Linux. Any USB adapter that uses these chipsets will most likely work with Kali.
Atheros AR9271
Ralink RT3070
Ralink RT3572
Realtek 8187L (Wireless G adapters)
Alfa adapters continue to dominate Pen Testing in 2015. Here are the top Kali Linux compatible wireless USB adapters with links to Amazon and AliExpress if available.
The AWUS036H is where I started – it’s a great adapter, but showing it’s age. It’s only a G adapter, and ideally you need an N adapter.
g = 54 mbps at 2.4 ghz
n = 300 mbps at 5 ghz
Most routers these days are n type routers. So you’d want to go for an adapter that can attack them.
Don’t buy anything related to signalking – its’ useless!
Here’s another link that details the chipsets used.
http://www.inkthat.us/kali-linux/best-kali-linux-compatible-usb-wireless-adapters/
Have fun!
LikeLike
Tyler,
Found this forum post – which debates alfa adapters
https://forums.kali.org/archive/index.php/t-4327.html
AWUS036NHA (my favourite)
excellent packet injecter
most access points had moderate signal strength but was able to connect to Most AP that had weak signals (-91dBm)
http://www.cyberprogrammers.net/2015/09/best-usb-wireless-adapterscards.html
So the conclusion seems to be the newer AWUS036 NHA is the best at packet injection at the moment.
https://www.youtube.com/watch?v=5Sfbr5AAnhg
LikeLike
Here’s a video of the two different chipsets in action
The AWUS 036 NHA is demonstrated to detect more networks – and to work with weaker signals.
https://www.youtube.com/watch?v=Y0_auDg1KaM
LikeLike
Thank you so much for your help! Looks like I have a bit of homework before making a purchase! Will let you know which one I go with!
Once I receive it, I’m sure that Ill be reaching out!
Thanks again!
Tyler
LikeLike
Yay! It’ll be great to hear how you get on.
You asked great questions, so you’ll be superb at pen testing.
LikeLike
Indeed the chipset and drivers matters for wifi adapters to be compatible with Kali. If you run kali as VM, then the adapter must be compatible with the host OS as well.
TP-Link TL-WN722N (AR9271 Chipset) and Alfa AWUSO36NH (RT3070 Chipset) are the two best options for kali linux. If you are on budget go for TP-Link.
LikeLike
Hi uwnthesis! I just recieved my ALFA AWUS036NH. Very excited to get started! Having some issues early on though. The first being that I run a macbook air with cd/dvd drive so that makes it difficult to install the adapter! Do you know of anywhere that I can download the driver utility software for a mac running El Capitan? Thanks! If you also know of an excellent guide to get started with Wi-Fi hacking, please send me the link! Hope to be in touch soon! Thanks for your help.
Cheers, Tyler
LikeLike
Hi Tyler,
Wifi cracking is such fun.
Try out “Fern” wifi hacking tool as one of the easiest. Use a WEP router, then a router with WPS on it – and let FERN crack the key for you. 🙂
LikeLike
Hii, would you be willing to crack this hash for me?
78df07b5ecedd34aece6c84d7c13356d
I simply have no idea how it works, but i really need my password back 😦
I’d appreciate it a lot!
LikeLike
Hi Sarah,
I’ve tried this as an MD5, SHA1 and an NTLM hash as its not that. Any idea what type of hash it is?
You can always submit your hash to http://www.hashkiller.co.uk
they will decrypt your hashes for free.
https://forum.hashkiller.co.uk/topic-view.aspx?t=12255&m=94981#94981 – but make sure that you change your password straight after.
LikeLike
Hi Sarah,
I’m pretty sure that your password was not hashed using MD5.
78df07b5ecedd34aece6c84d7c13356d MD5 : 94bfbfb41eba4e7150261511f4370f65
Any idea of the correct hashing algorithm?
LikeLike